A Closer Look at Falcon
Falcon is a winner of NIST’s six-year post-quantum cryptography standardization competition. Based on the celebrated full-domain-hash framework of Gentry, Peikert and Vaikuntanathan (GPV) (STOC’08), Falcon leverages NTRU lattices to achieve the most compact signatures among…
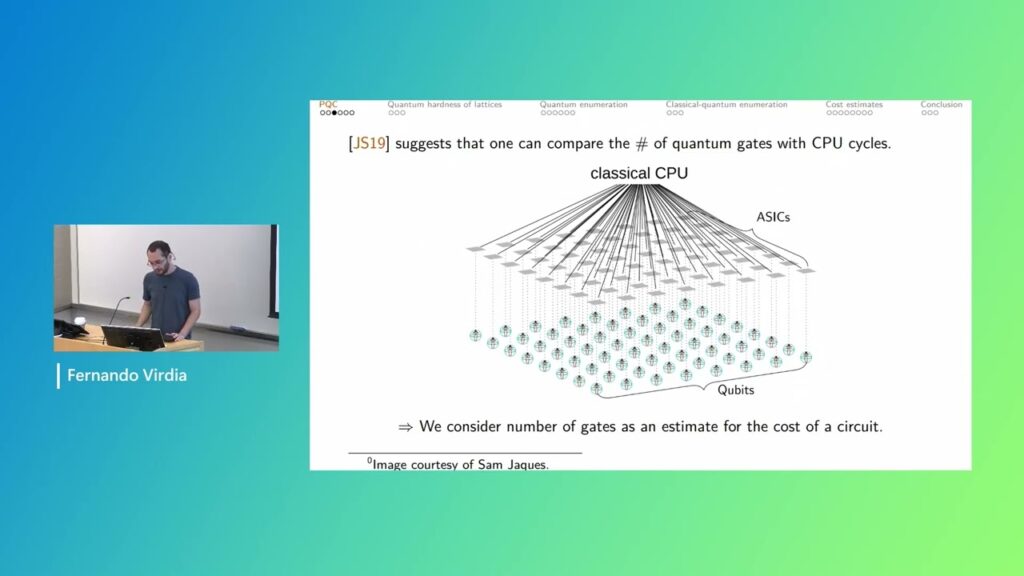
Quantum Lattice Enumeration in Limited Depth, Fernando Virdia
In 2018, Aono, Nguyen, and Shen (ASIACRYPT 2018) proposed to use quantum backtracking algorithms (Montanaro, TOC 2018; Ambainis and Kokainis, STOC 2017) to speedup lattice point enumeration. Aono et al.’s work argued that quantum walk…
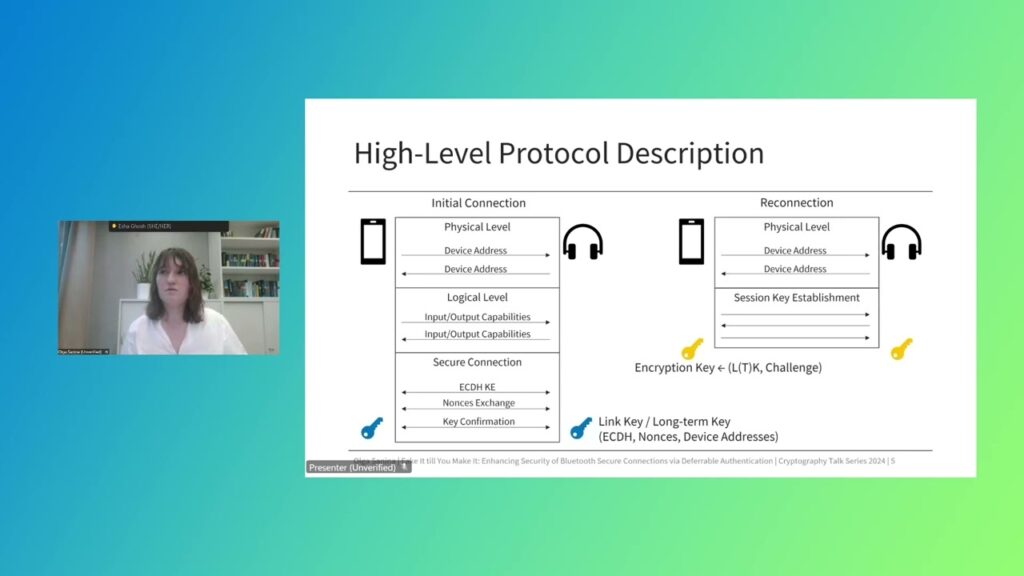
Fake It till You Make It: Enhancing Security of Bluetooth Secure Connections via Deferrable Authentication
The Bluetooth protocol for wireless connection between devices comes with several security measures toprotect confidentiality and integrity of data. At the heart of these security protocols lies the SecureSimple Pairing, wherewith the devices can negotiate…
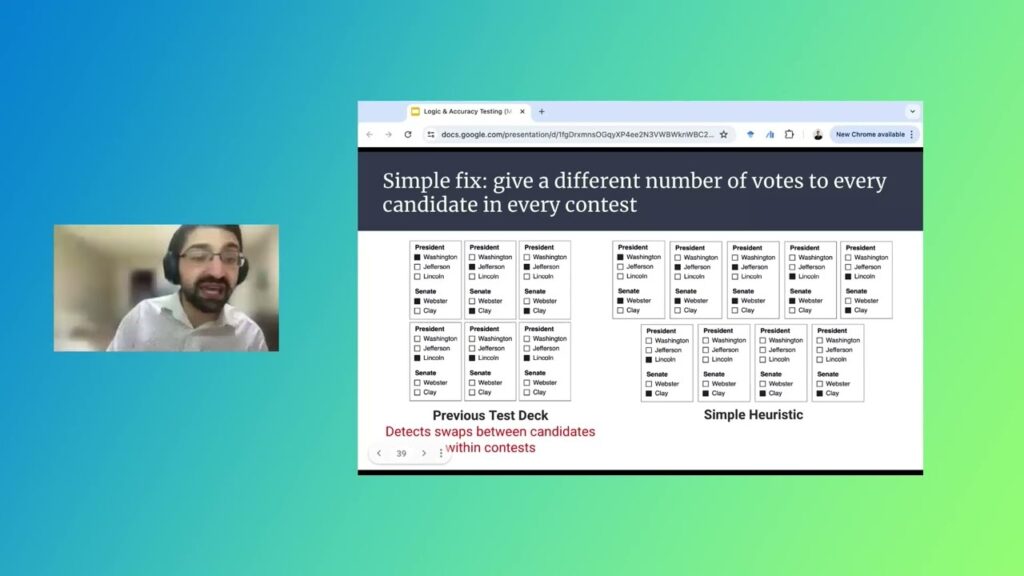
Improving the Security of United States Elections with Robust Optimization
For more than a century, election officials across the United States have inspected voting machines before elections using a procedure called Logic and Accuracy Testing (LAT). This procedure consists of election officials casting a test deck…
Research Focus: Week of December 2, 2024
Can a new SOS-RMT protocol enable more efficient CL-MPC?; A fair-by-design, cloud-based algorithmic trading platform; LLM2CLIP unlocks richer visual representation; New technique enhances Low-Rank Adaptation’s expressiveness, generalization capabilities.
Preventing side-channels in the cloud
Sophisticated side-channel attacks present new security challenges for cloud providers. Learn how Microsoft is exploring defenses against emerging attacks with principled microarchitectural isolation: