Putting Information Sharing into Context: New Whitepaper Offers Framework for Risk Reduction
The nearly incessant drumbeat of cybersecurity incidents over the past weeks and months has brought about renewed interested in information sharing across the technical and political spheres. For example, earlier this month the White House proposed legislation to encourage information sharing which President Obama also referred to in his State of the Union address. When it comes to cybersecurity, the right information exchanged or shared at the right time can enable security professionals and decision makers to reduce risks, deflect attacks, mitigate exploits and enhance resiliency. In this case, forewarned really can mean forearmed.
Information sharing is not a novel idea. A number of initiatives around the world have been in place and working successfully for some time. For example, here at Microsoft we have a program in place that gives security software providers early access to vulnerability information so that they can provide updated protections to customers faster. From this and other programs of various sizes we have learned that despite the increased focus on collective action from both private practitioners and policy makers around the world, effective information sharing is not an easy undertaking. It requires clear definitions and objectives rather than solely words of encouragement, or mandatory requirements. Furthermore, it is all too often viewed simply as a goal in and of itself rather than as a mechanism for improving security, cybersecurity assessment, and risk management. Finally, and from the public-private partnership perspective most pressingly, information sharing can quickly expand into controversies involving originator control, trust, transparency, privacy and liability.
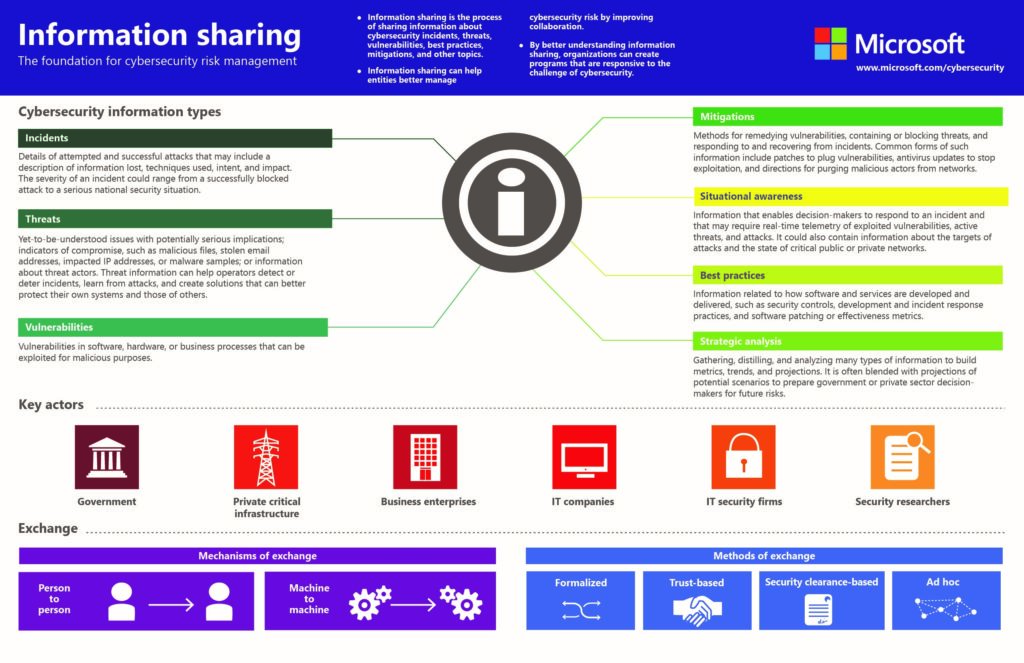
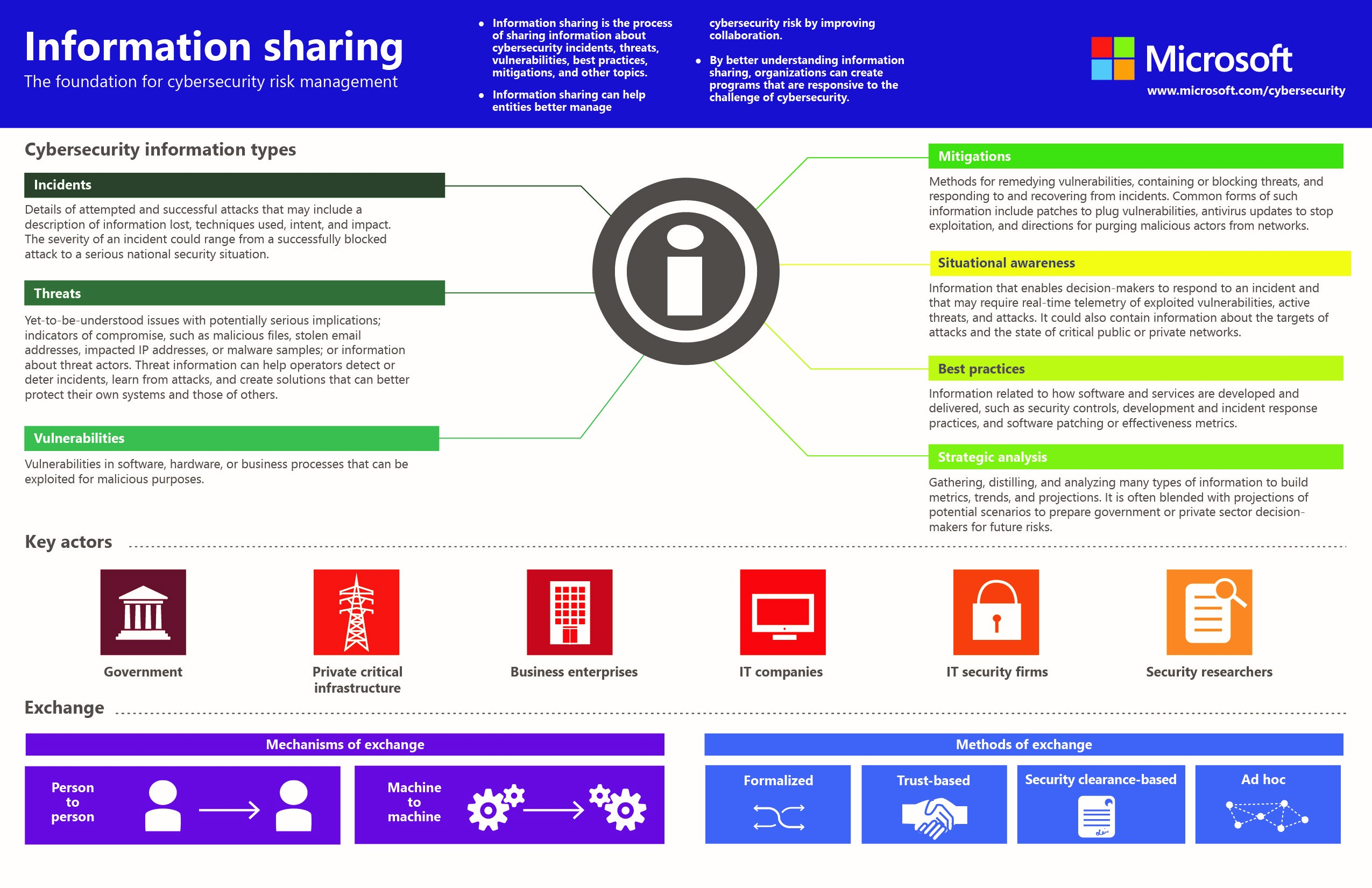
To help put this complex issue into context, today we are releasing a new white paper: A framework for cybersecurity information sharing and risk reduction. Leveraging Microsoft’s decades of experience in managing security for our products, infrastructure, and customers, the paper provides a taxonomy for information exchanges including types, actors, and methods. We believe that understanding how to incentivize information sharing and how to better harness the practice for risk reduction can help move policy and strategy debates forward and support better defence of cyber assets and infrastructure. The paper concludes with a discussion of best practices and seeks to lay the groundwork for a more formalized, collaborative approach to information sharing and implementing exchanges through a set of recommendations. I hope that it can serve as a relevant and timely guide for anyone with responsibility for developing new ideas and solutions for information exchanges.