The 24th edition of the Microsoft Security Intelligence Report (SIR) is now available. And this year, I’m thrilled to share that not only can you download the PDF, but you can also visit an online, interactive version that provides tools to filter and deep dive into the data. This edition of the report is a reflection on last year’s security events and includes an overview of the security landscape, lessons learned from the field, and recommended best practices. I know you may find some of the trends, such as the increase in cryptocurrency mining and supply chain activity, worrisome. But I also hope you’re encouraged to learn that the defensive techniques we’ve taken as a security community are paying off: there is good evidence that bad actors have been forced to change their tactics.
To create this report, the SIR team culled core insights and key trends out of a year’s worth of data from multiple, diverse sources. We analyzed the 6.5 trillion security signals that go through the Microsoft cloud every day. We gathered insights from thousands of security researchers based around the world, and we learned lessons from real-world experiences, like the Ursnif campaign and the Dofoil coin-miner outbreak. There is a lot going on, but the SIR team distilled the data down into four key trends:
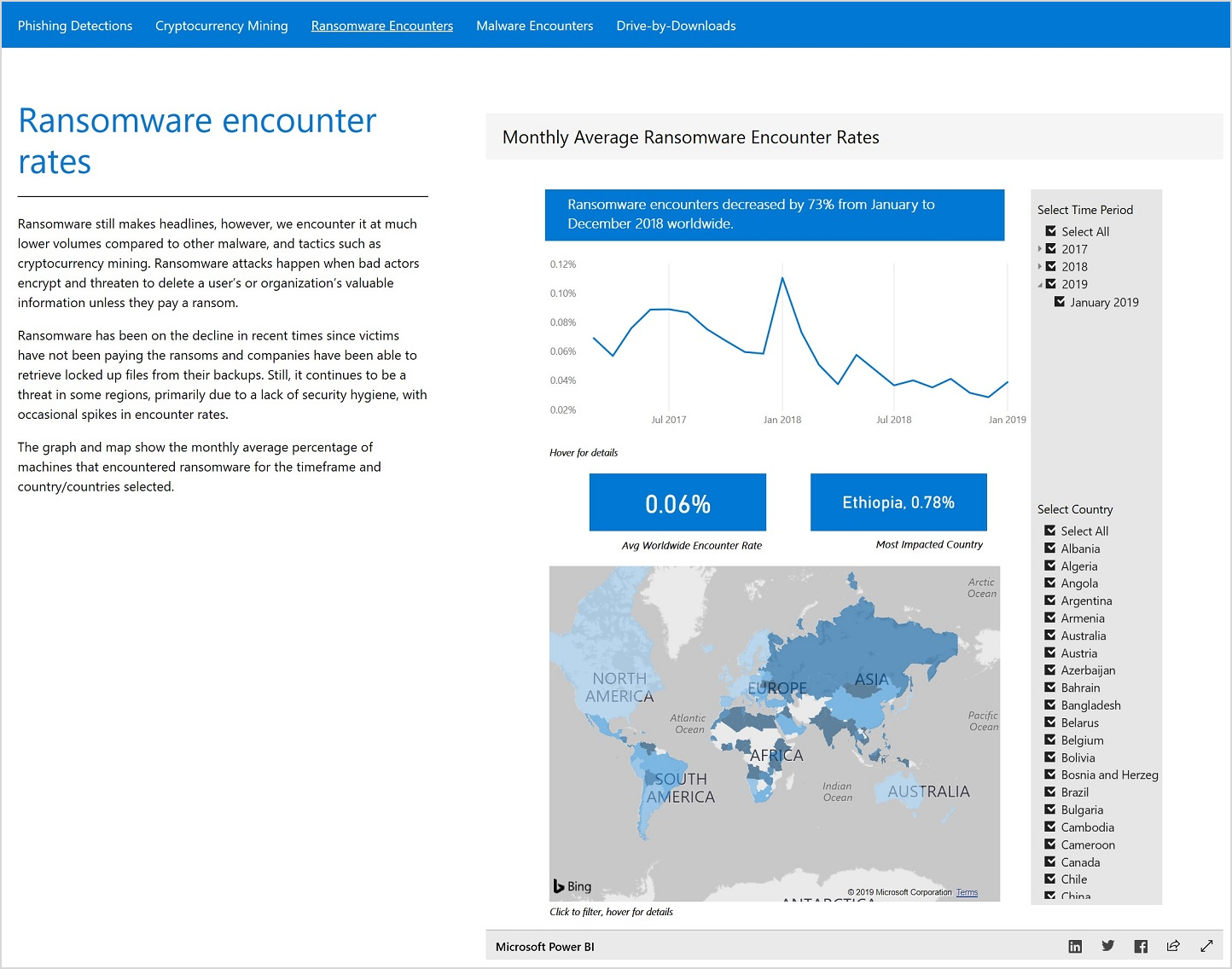
- Ransomware attacks are on the decline.
- Cryptocurrency mining is prevalent.
- Software supply chains are at risk.
- Phishing remains a preferred attack method.
Ransomware attacks are on the decline
The decline of ransomware attacks that we saw in the 2018 data is a great example of how the security community is pushing bad actors to adjust. Just last year, we highlighted the large threat that ransomware played in the 2017 data, so this decline is notable. We believe that attackers have shifted from this highly visible method to more stealth attacks because users have gotten smarter about how they respond.
Cryptocurrency mining is prevalent
The decline in ransomware is good news; however, on the flip side we are seeing cryptocurrency mining to be prevalent. This is one of the methods that attackers have deployed in lieu of ransomware. Mining coins profitably requires an immense amount of computing power to perform complex calculations, so attackers install malware on users’ computers to “steal” the necessary computing power. The SIR report provides a great overview of how cryptocurrency works and other factors driving this trend.
Software supply chains are at risk
Software supply chain attacks are another trend that Microsoft has been tracking for several years. One supply chain tactic used by attackers is to incorporate a compromised component into a legitimate application or update package, which then is distributed to the users via the software. These attacks can be very difficult to detect because they take advantage of the trust that users have in their software vendors. The report includes several examples, including the Dofoil campaign, which illustrates how wide-reaching these types of attacks are and what we are doing to prevent and respond to them.
Phishing remains the preferred method of attack
It’s probably not surprising that phishing continues to be a popular method of attack, and we expect that to continue for the foreseeable future. The good news: much like ransomware, bad actors have shifted tactics in response to the more sophisticated tools and techniques that have been deployed to protect users. We uncovered a lot of details about these new phishing methods that we hope you find useful in your fight to defend against them.
Learn more
When I was a practitioner, I sought out reports like these to help me better understand attacker techniques and plan my defenses accordingly. I hope you find the insights, tips, and best practices that we’ve pulled together just as helpful. Download volume 24 of the Microsoft Security Intelligence Report and then dig into the data specific to your region in the interactive website. The site will be updated monthly, so you can keep up with emerging data and insights throughout the year.
Also, later in March, join me and my colleague, Jonathan Trull, for a webinar where we’ll dissect these trends in more detail and share best practices to help you protect your organization.
The SIR serves to share some of the intelligence and insights that Microsoft generates as part of our broader security operations work, but it is not the whole story. Please also make sure to check out today’s announcements on new Microsoft security innovations aimed at helping defenders capitalize on the latest security intelligence and protections to help them stay ahead in the evolving cybersecurity landscape.