Credential theft
Refine results
Topic
Products and services
Publish date
-
 If you are working on initiatives to secure your privileged accounts (and I hope you are), this post is designed to help.
If you are working on initiatives to secure your privileged accounts (and I hope you are), this post is designed to help. -
Hawkeye Keylogger – Reborn v8: An in-depth campaign analysis
Hawkeye Keylogger is an info-stealing malware that’s being sold as malware-as-a-service. -
How to mitigate rapid cyberattacks such as Petya and WannaCrypt
Because of how critical security hygiene issues have become and how challenging it is for organizations to follow the guidance and the multiple recommended practices, Microsoft is taking a fresh approach to solving them. -
Overview of Petya, a rapid cyberattack
In the first blog post of this 3-part series, we introduced what rapid cyberattacks are and illustrated how they are different in terms of execution and outcome. -

Now you see me: Exposing fileless malware
Attackers are determined to circumvent security defenses using increasingly sophisticated techniques. -
Ransomware 1H 2017 review: Global outbreaks reinforce the value of security hygiene
The trend towards increasingly sophisticated malware behavior, highlighted by the use of exploits and other attack vectors, makes older platforms so much more susceptible to ransomware attacks. -
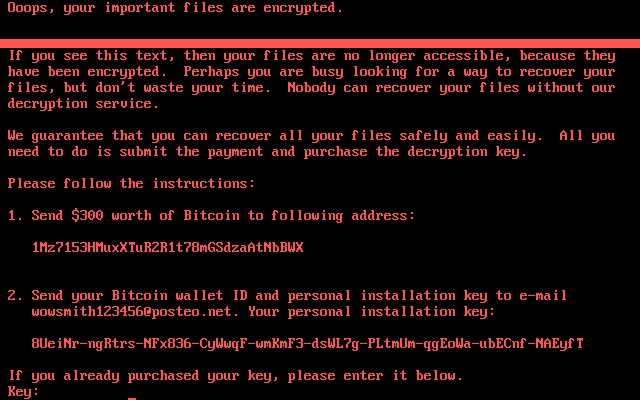
New ransomware, old techniques: Petya adds worm capabilities
On June 27, 2017 reports of a ransomware infection began spreading across Europe. -
The two-pronged approach to detecting persistent adversaries
Advanced Persistent Threats use two primary methods of persistence: compromised endpoints and compromised credentials. -
Use Security Education and Awareness Programs to Your Advantage
This post is authored by Jonathan C. Trull, Worldwide Executive Cybersecurity Advisor, Enterprise Cybersecurity Group Most of today’s media coverage, internal security budgets, and venture capital dollars are focused on new and exciting technologies, such as next-generation endpoint solutions, user behavior analytics, and others. -
KRBTGT Account Password Reset Scripts now available for customers
Although pass-the-hash credential theft and reuse attacks aren’t new, more recently security researchers have been focusing on attack methods for Kerberos authentication. -
7 Precautions for Protecting Against Perpetrators
Cyberattacks and data breaches continue to dominate the news globally. -
Enterprise Threat Encounters: Scenarios and Recommendations – Part 1
Many of the IT Professionals that contact our customer service and support group have common questions related to security incidents and are seeking guidance on how to mitigate threats from determined adversaries.