Cryptocurrency mining—once considered no more than a nuisance, a relatively benign activity that was a drain on machine resources—has been on the rise in recent years. This increase in cryptocurrency mining activity is driven by the increasing value of cryptocurrencies like Bitcoin, the growth in popularity of different kinds of cryptocurrency (Ethereum, Litecoin, and Dogecoin), and the volatility in these markets. As cryptocurrency prices rise, many opportunistic attackers now prefer to use cryptojacking over ransomware. The risks for organizations have increased, as attackers deploy coin miners as a payload for malware campaigns. According to recent research from Avira Protection Labs, there was a 53 percent increase in coin miner malware attacks in Q4 2020 compared to Q3 2020.
In addition, with malware evolving over the years to evade typical anti-malware defenses, detecting coin miners has become increasingly more challenging.
This rising threat is why Microsoft and Intel have been partnering to deliver technology that uses silicon-based threat detection to enable endpoint detection and response (EDR) capabilities in Microsoft Defender for Endpoint to better detect cryptocurrency mining malware, even when the malware is obfuscated and tries to evade security tools.
Intel Threat Detection Technology in Microsoft Defender for Endpoint
Today, we are announcing the integration of Intel Threat Detection Technology (TDT) into Microsoft Defender for Endpoint, an addition that enhances the detection capability and protection against cryptojacking malware. This builds on our existing partnership and prior collaboration to integrate Intel’s Accelerated Memory Scanning with Defender.

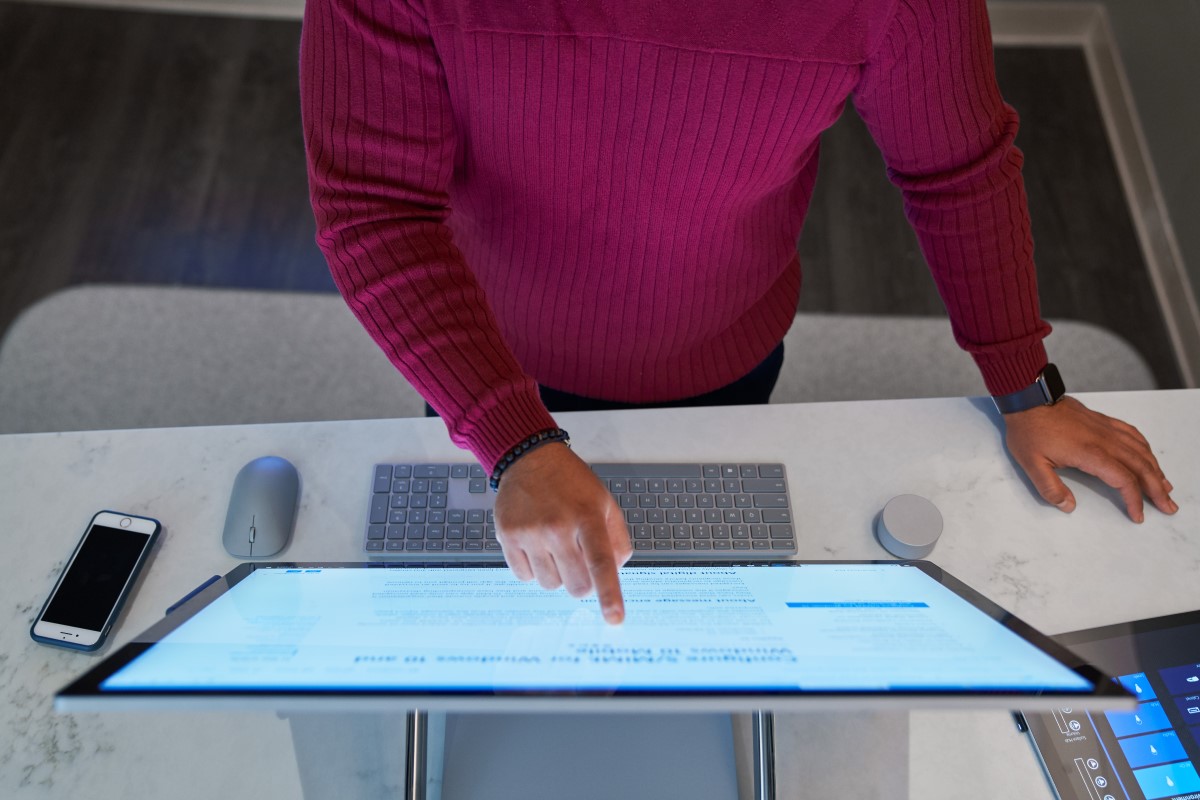
Figure 1: CoinMiner alert from Microsoft Defender for Endpoint.
Intel TDT applies machine learning to low-level hardware telemetry sourced directly from the CPU performance monitoring unit (PMU) to detect the malware code execution “fingerprint” at runtime with minimal overhead. TDT leverages a rich set of performance profiling events available in Intel SoCs (system-on-a-chip) to monitor and detect malware at their final execution point (the CPU). This happens irrespective of obfuscation techniques, including when malware hides within virtualized guests, without needing intrusive techniques like code injection or performing complex hypervisor introspection. TDT can further offload machine learning inference to the integrated graphics processing unit (GPU), enabling continuous monitoring with negligible overhead. While we haven’t seen any performance issues with the current deployments, we plan to enable the GPU offloading capabilities of Intel TDT in the near future.
This technology is based on telemetry signals coming directly from the PMU, the unit that records low-level information about performance and microarchitectural execution characteristics of instructions processed by the CPU. Coin miners make heavy use of repeated mathematical operations and this activity is recorded by the PMU, which triggers a signal when a certain usage threshold is reached. The signal is processed by a layer of machine learning which can recognize the footprint generated by the specific activity of coin mining. Since the signal comes exclusively from the utilization of the CPU, caused by execution characteristics of malware, it is unaffected by common antimalware evasion techniques such as binary obfuscation or memory-only payloads.
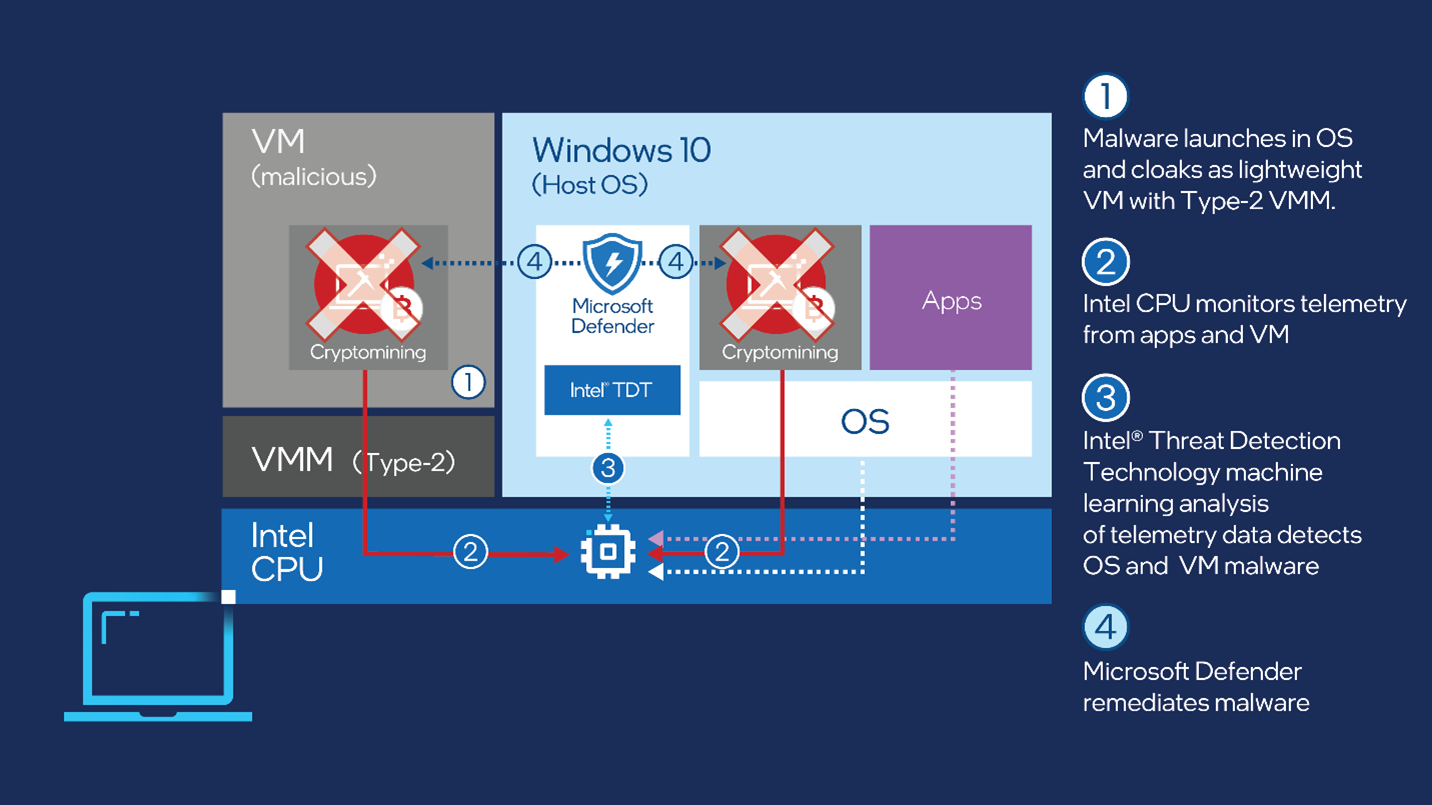
Figure 2: Diagram showing how Intel TDT and Microsoft Defender detect and remediate malware.
Even though we have enabled this technology specifically for cryptocurrency mining, it expands the horizons for detecting more aggressive threats like side-channel attacks and ransomware. Intel TDT already has the capabilities for such scenarios, and machine learning can be trained to recognize these attack vectors.
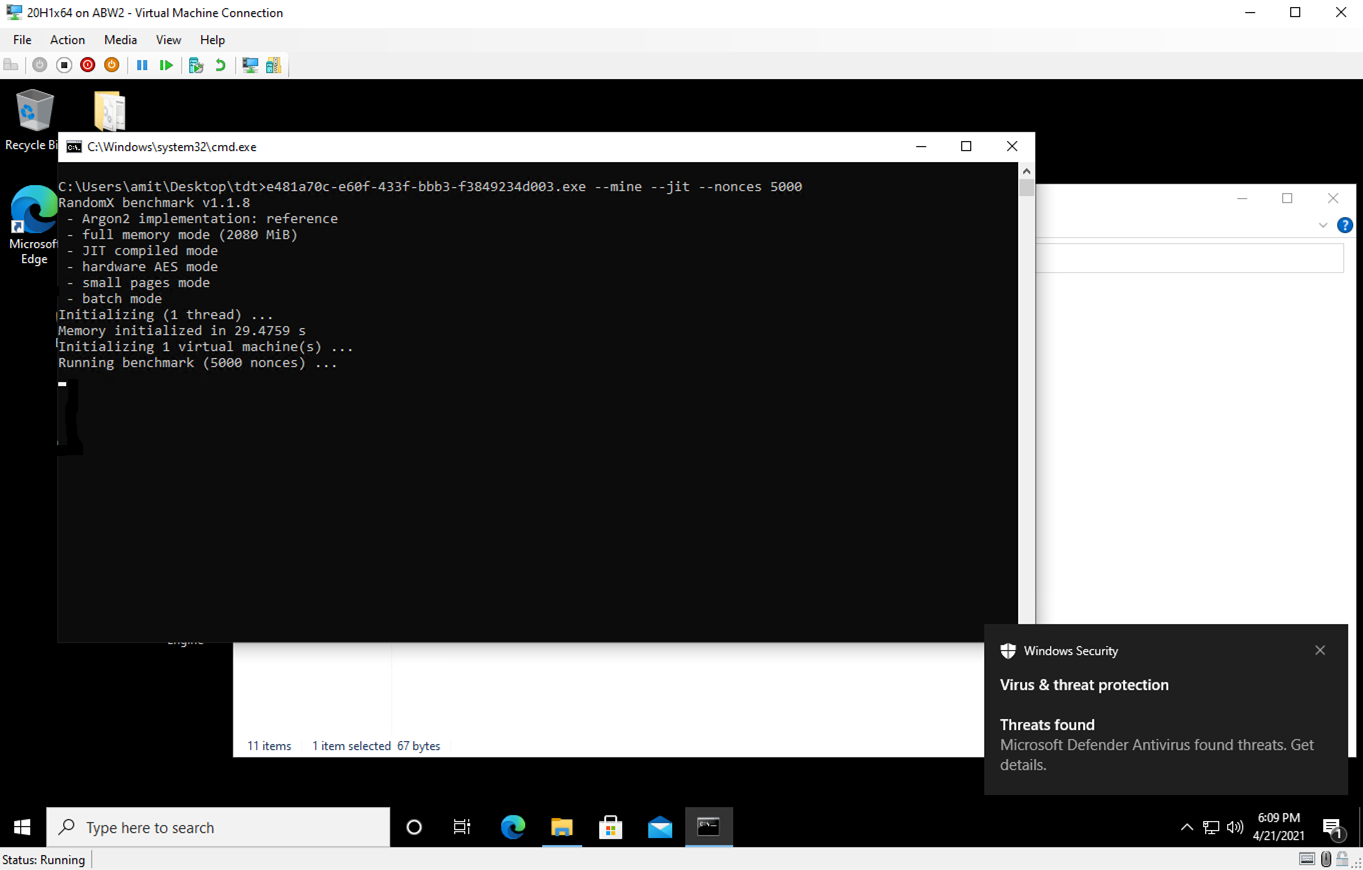
Figure 3: Intel TDT and Microsoft Defender detect malware. The user is notified of a threat via a Windows Security notification.
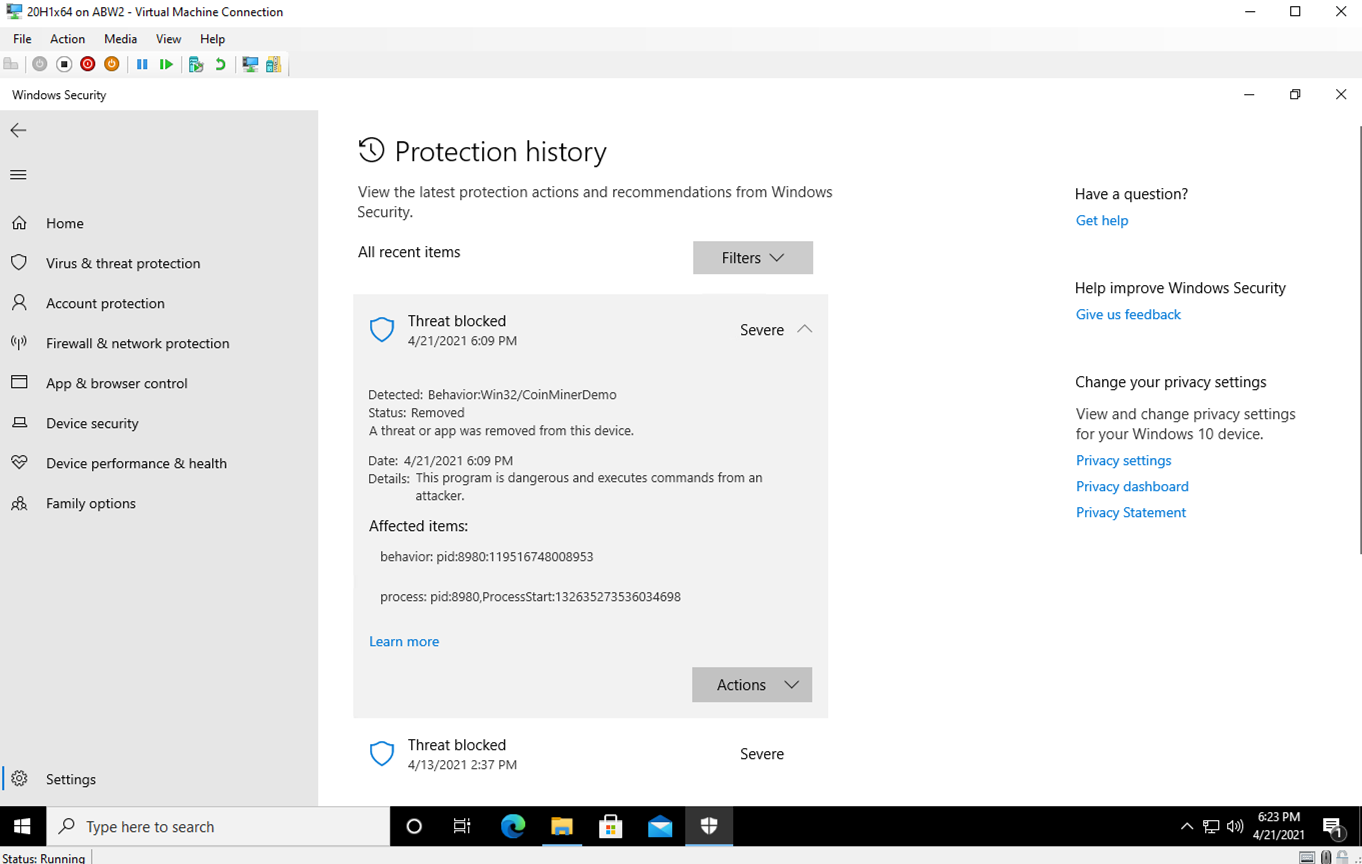
Figure 4: Windows security protection history showing CoinMiner threat blocked. Detected with Intel TDT and Microsoft Defender.
This technology doesn’t require any additional investments, IT configuration, or installation of agents. The Microsoft Defender for Endpoint and Intel TDT integrated solution works natively with Intel® Core™ processors and the Intel vPro® platform, 6th Generation or later.
Since the main signal used for this detection capability comes right from the hardware (the Intel CPU), it can detect coin miners running inside unprotected virtual machines and other containers. This demo video showcases how, in such a scenario, Microsoft Defender for Endpoint can stop the virtual machine itself or report virtual machine abuse, thus preventing the spread of an attack as well as saving resources. This is one step towards agentless malware detection, where the “protector” can protect the asset from the “attacker” without having to be in the same OS.
As we enable the technology on more and more supported platforms, we are getting valuable machine learning telemetry back, which informs and makes the existing models better and more effective.
As organizations look to simplify their security investments, we’re committed to our focus on built-in platform-based security technologies, delivering a best-of-breed and streamlined solution that empowers defenders to elevate their security and protect their organizations. This partnership is part of Microsoft’s investment into collaborations with original equipment manufacturers (OEMs) and technology partners. We’re working closely with chipmakers to always explore new possibilities for hardware-based defense hardening and deliver robust and resilient protection against cyber threats.
Learn more
For additional details, please read Intel’s News Byte.
Microsoft Defender for Endpoint is an industry-leading, cloud-powered endpoint security solution offering vulnerability management, endpoint protection, endpoint detection and response, and mobile threat defense. With our solution, threats are no match. If you are not yet taking advantage of Microsoft’s unrivaled threat optics and proven capabilities, sign up for a free trial of Microsoft Defender for Endpoint today.
To learn more about Microsoft Security solutions visit our website. Bookmark the Security blog to keep up with our expert coverage on security matters. Also, follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
Amitrajit Banerjee, Andrea Lelli, Gowtham Animi Reddy, Karthik Selvaraj, Kelvin Chan, Shweta Jha
Microsoft Defender for Endpoint Team