Microsoft Defender
Microsoft Defender helps prevent, detect, and respond to attacks across devices, identities, apps, email, data, workloads, and clouds. Explore threat intelligence, capabilities, and real-world guidance to help you get more out of Defender.
Refine results
Topic
Products and services
Publish date
-
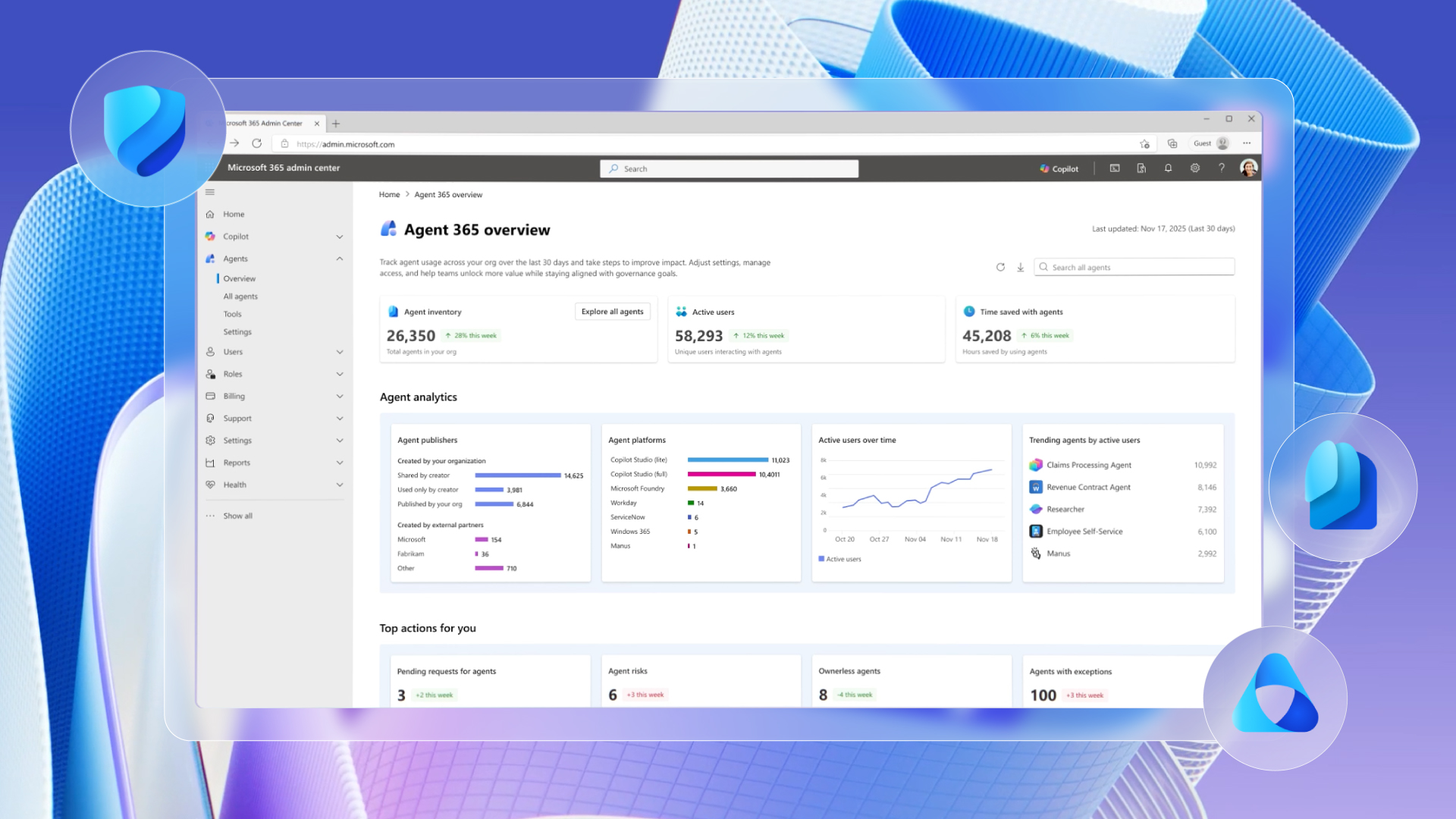
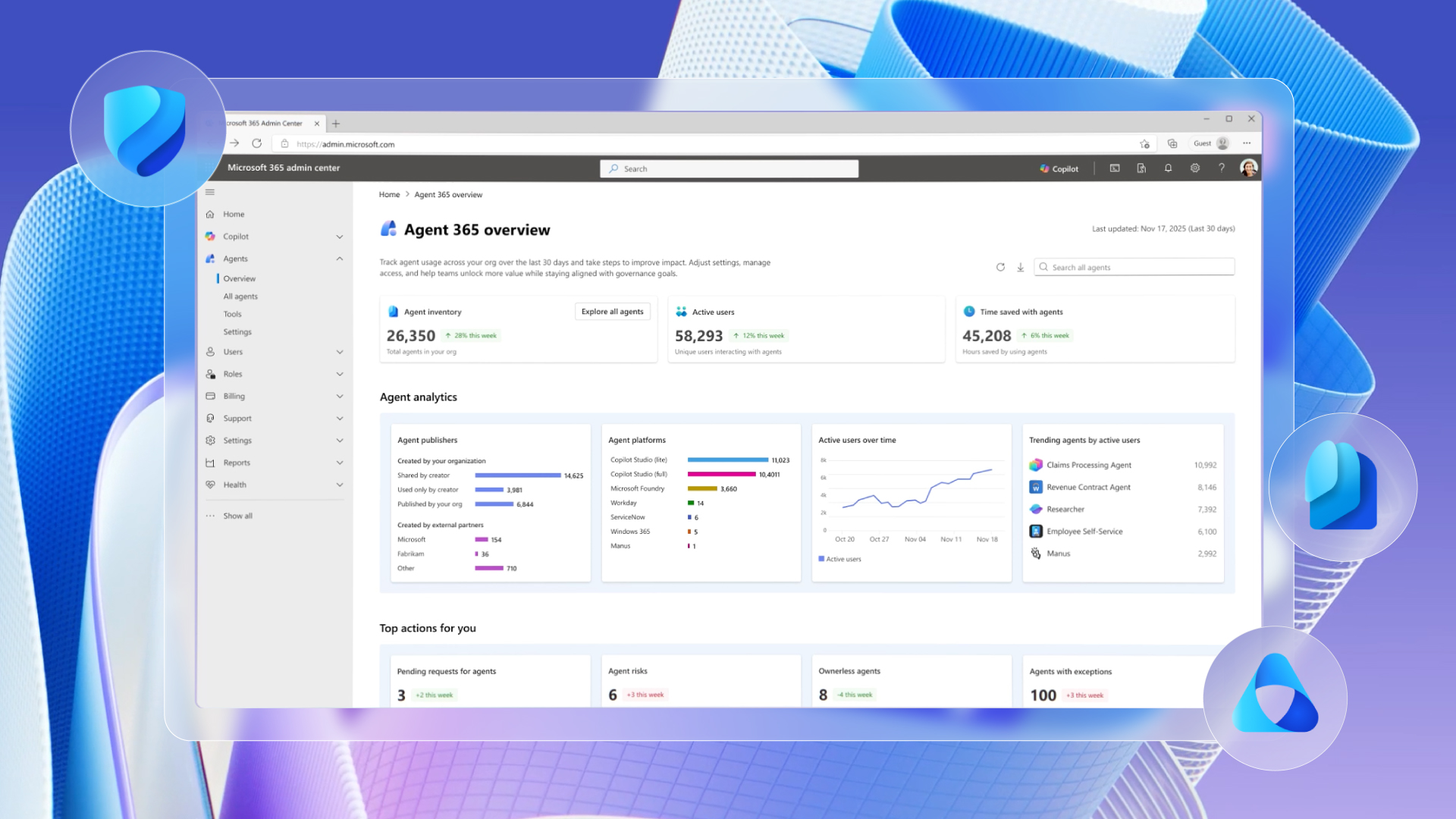 We are announcing the next step to make Frontier Transformation real for customers across every industry with Wave 3 of Microsoft 365 Copilot, Microsoft Agent 365, and Microsoft 365 E7: The Frontier Suite.
We are announcing the next step to make Frontier Transformation real for customers across every industry with Wave 3 of Microsoft 365 Copilot, Microsoft Agent 365, and Microsoft 365 E7: The Frontier Suite. -

Contagious Interview: Malware delivered through fake developer job interviews
The Contagious Interview campaign weaponizes job recruitment to target developers. -

From transparency to action: What the latest Microsoft email security benchmark reveals
The latest Microsoft benchmarking data reveals how Microsoft Defender mitigates modern email threats compared to SEG and ICES vendors. -

Secure agentic AI end-to-end
In this agentic era, security must be woven into, and around, every layer of the AI estate. -

Guidance for detecting, investigating, and defending against the Trivy supply chain compromise
Threat actors abused trusted Trivy distribution channels to inject credential‑stealing malware into CI/CD pipelines worldwide. -

Mitigating the Axios npm supply chain compromise
On March 31, 2026, the popular HTTP client Axios experienced a supply chain attack, causing two newly published npm packages for version updates to download from command and control (C2) that Microsoft Threat Intelligence has attributed to the North Korean state actor Sapphire Sleet. -

Cookie-controlled PHP webshells: A stealthy tradecraft in Linux hosting environments
Cookie-gated PHP webshells use obfuscation, php-fpm execution, and cron-based persistence to evade detection in Linux hosting environments. -

Storm-1175 focuses gaze on vulnerable web-facing assets in high-tempo Medusa ransomware operations
The financially motivated cybercriminal threat actor Storm-1175 operates high-velocity ransomware campaigns that weaponize recently disclosed vulnerabilities to obtain initial access, exfiltrate data, and deploy Medusa ransomware.